Early 2025 I was asked to carry out an end to end build review and a full security assessment of a laptop. The brief was similar to a stolen laptop scenario, assume physical access, assess what could realistically be achieved, and report on the risks. This was not new territory for the client, they had commissioned many of these assessments over the years. What was different this time was that they had recently purchased a new fleet of Lenovo X1 Carbon laptops, and we wanted to push things further than we had before.
As part of the engagement, we asked whether we could look beyond software and configuration, and spend time on the hardware side. The client agreed.
Once the laptop was opened, one of the first things noticed was a physical tamper switch on the internal hardware. These switches are sometimes configured to prevent the device from booting if the case has been opened, acting as a basic physical intrusion detection mechanism.
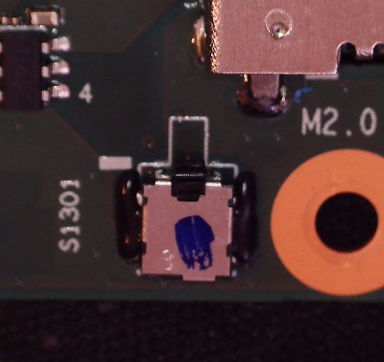
To avoid triggering any protective behaviour during testing, the switch was carefully hot glued in place. This allowed further inspection without causing the system to lock or fail to boot.
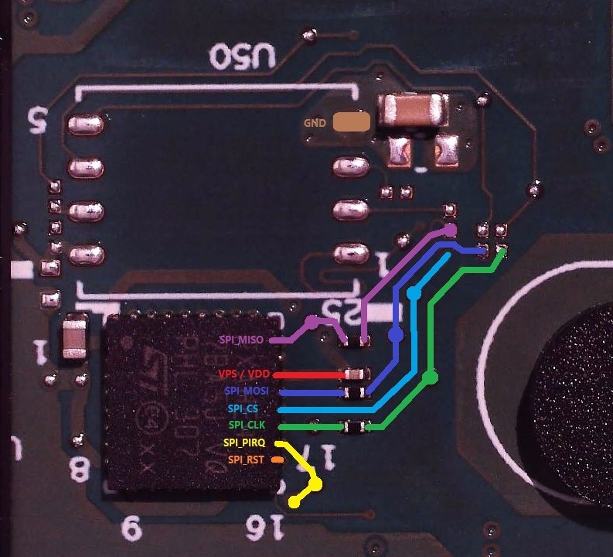
Continuing the teardown, it became clear that the system was using a discrete TPM rather than firmware TPM. The chip in question was an ST33TPHF2XSPI, communicating with the rest of the platform over SPI. This immediately raised interest, as SPI based TPMs have a long history of being sniffable under the right conditions.
Tracing the PCB revealed that the SPI lines between the TPM and the rest of the system were routed to accessible test pads on the motherboard.
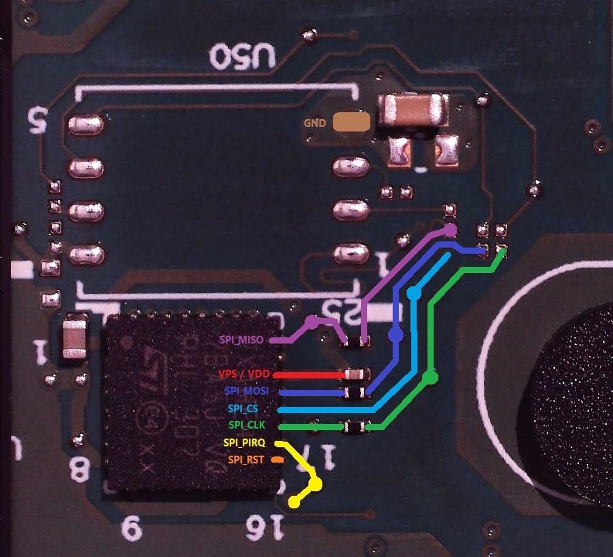
Thin 0.1 mm wires were soldered to the relevant SPI pins, MISO, MOSI, CLK and CS. These were then secured with hot glue to prevent detachment while reassembling the laptop.
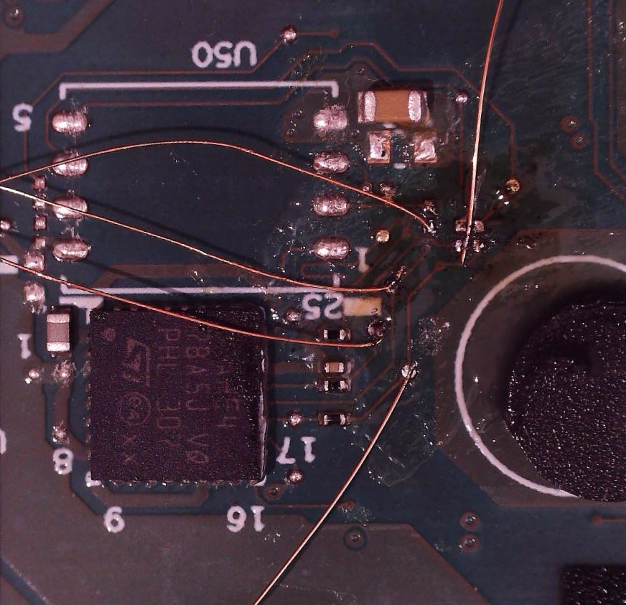
At this point the laptop was reassembled into a fully working state. It booted normally and reached the Windows 11 login screen without any obvious signs of tampering.
With the hardware access in place, a logic analyser, in this case a Saleae Logic Pro 16, was connected to the SPI lines. The goal was to observe the TPM communication during boot and determine whether the BitLocker Volume Master Key was being released over the bus.
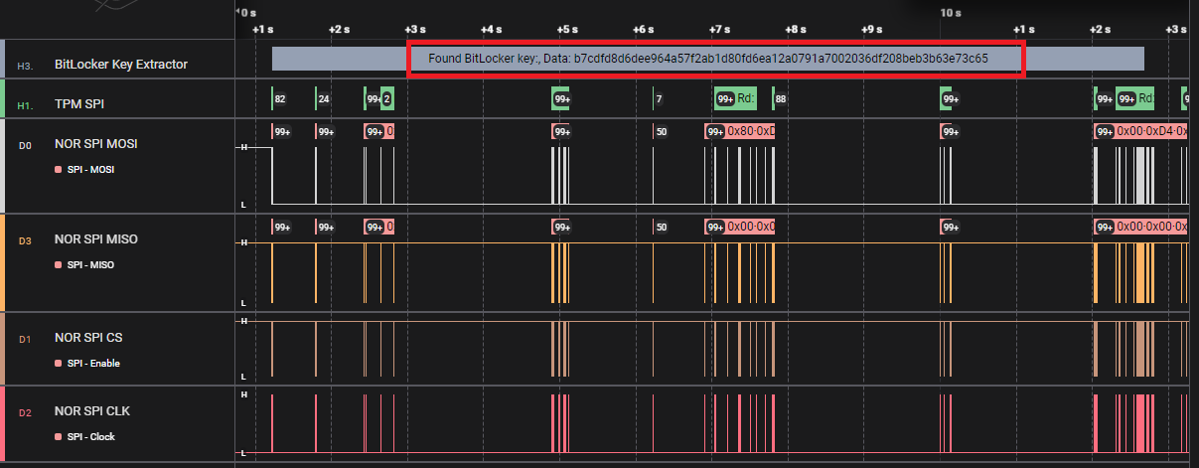
During early boot, the TPM did exactly what it was designed to do. It released the BitLocker VMK to the platform once its policy checks were satisfied. Because this was a TPM only BitLocker configuration, no pre boot authentication was required, and the key material traversed the SPI bus in clear form.
The VMK was successfully extracted from the captured traces. With that key, the internal SSD could be decrypted offline using dislocker. From there it was possible to extract the SAM and SYSTEM hives and move on to further credential analysis and privilege escalation.
This was, to my knowledge, the first public extraction of a BitLocker VMK from a Lenovo X1 Carbon 2025 laptop running Windows 11 with a TPM 2.0 device.
What made this possible was not a single tool or guide. It was the result of piecing together dozens of blog posts, research papers, GitHub repos, conference talks and random social media threads. The information was out there, but it was fragmented, inconsistent, and often hard to find again when you needed it.
That experience is what led me to create the TPM-Sniffing repository.
The idea was simple. Create a centralised resource that documents which machines have been tested, which TPMs they use, how they communicate, and which techniques have been shown to work. Not theory, not marketing claims, but real world research backed by references.
One of the best parts of this so far has been the community response. People are contributing new machines, sharing fresh research, opening issues, and pushing updates as the landscape changes. It is a living resource, and that matters in a space where vendors and hardware designs evolve constantly.
This repo exists for two reasons. To show that these attacks are practical and relevant when physical access is in scope, and to give something back to the community that helped me get there in the first place. If it helps defenders model risk more accurately, or helps researchers get started faster, then it is doing its job.
Contributions are welcome, and I hope it continues to grow as more people explore this space.